Warroom
New Zealand Homeland Defense
4-Level Threat Scenario Simulation
Deep analysis of tactical details and defensive vulnerabilities across four extreme scenarios: Terrorist Attacks, Regional Conflicts, Major Power Surprise Attacks, and Unrestricted Warfare.
⚠️ DISCLAIMER: This article is purely a battle case analysis. Four attack scenarios are presented first; analyses of emergency defense measures, armament requirements, combat capabilities, and preventive measures will be updated subsequently.
Scenario 1: High-Intensity Terror Attack (The “Black Swan”)
Characteristics: Soft Targets, Hostage Taking, Political Propaganda
Tactical Expansion
Attackers do not seek a head-on collision with military/police forces initially. Instead, they exploit NZ’s open society, infiltrating as tourists or refugees in waves. Weapons are assembled domestically from disassembled maritime shipments or 3D-printed components.
-
▶
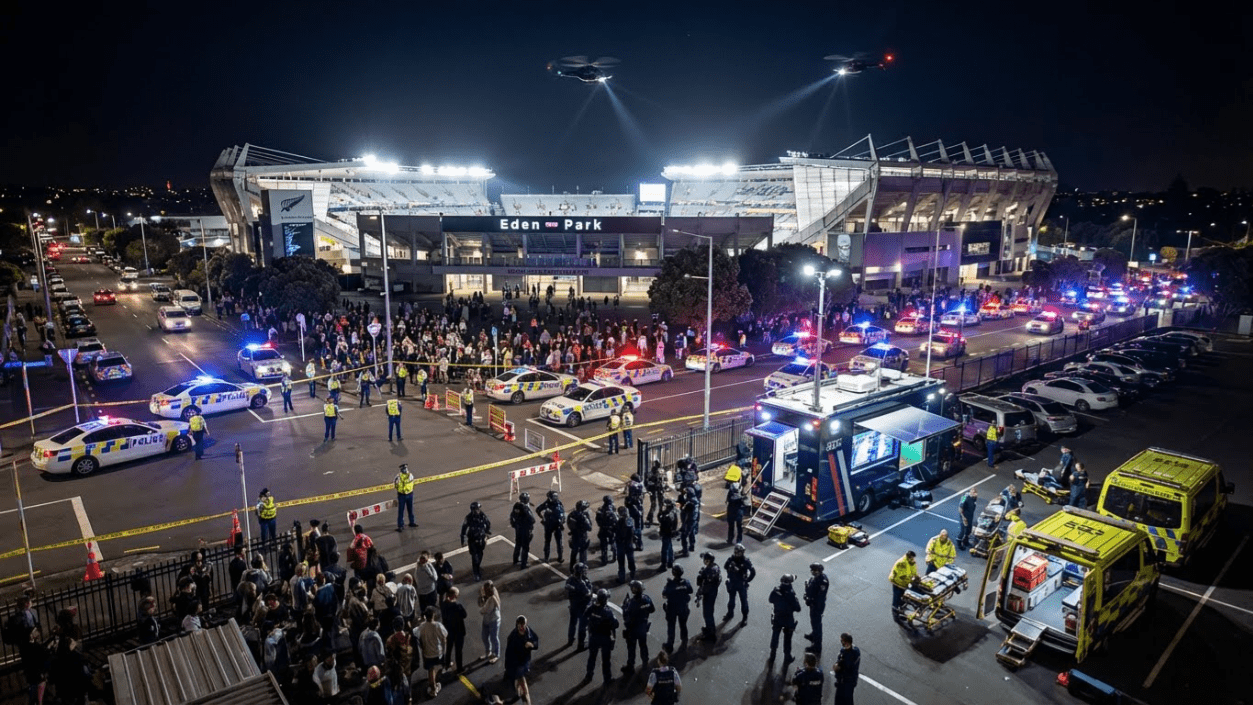
Target Selection: Eden Park (Auckland) major sporting events or Rhythm and Vines music festivals. These locations are densely populated, have relatively loose security checks, and are difficult to evacuate.
-
▶
Modus Operandi: Using paragliders or modified pickup trucks to ram perimeter defenses, combined with automatic rifle fire to create panic. Subsequently seizing core buildings (e.g., stadium VIP areas), taking hundreds of hostages, and planting Improvised Explosive Devices (IEDs) at exits.
-
▶
Political Demands: Utilizing live streams to demand NZ’s withdrawal from the “Five Eyes” alliance, or the release of specific extremist leaders detained in the Middle East/Asia.
Defensive Pain Points
- Delayed Response Time NZ SAS is based in South Auckland; mobilizing helicopters to remote festivals takes hours.
- Lack of Mass Casualty Capacity Hospitals cannot handle the simultaneous influx of hundreds of gunshot victims.
- Media Control Failure Terrorists utilize social media to livestream killings, causing psychological paralysis among the public.
Scenario 1: High-Intensity Terrorist Attack
THE BLACK SWAN EVENT
A deep simulation based on a large-scale event at Eden Park stadium coming under attack. It focuses on the attackers’ objectives, the consequences of missing contingency plans, the full counterterrorism response process, and national-level prevention strategies.
1. Attack Initiation and Strategic Objectives
Soft-target attacks, creating panic, and political coercion

Chaos Erupts Inside the Stadium
Terrorists infiltrate in disguise and use multi-point explosions to cut off exits.
Maximizing Panic (Mass Casualty)
The attackers deliberately select Eden Park or a large music festival as a “soft target”. Taking advantage of tens of thousands of people packed into a confined space, they conduct coordinated attacks (small-arms fire plus improvised explosive devices (IEDs)) at multiple points, aiming to paralyze on-site order within minutes, trigger stampedes and large-scale casualties, and delay the entry of emergency medical teams.
Political Coercion and Global Live Broadcast
A core cell quickly seizes the broadcast room or VIP area and controls high-value hostages. They use the venue’s network to broadcast the situation globally, issuing political demands such as the release of specific prisoners or a change in New Zealand’s foreign-policy stance (for example, withdrawing from an international alliance). Visual impact is used to escalate a single violent event into a full-scale national political crisis.
2. Importance of Contingency Planning and Network Isolation
Life-and-death decisions and information control in the golden minutes
The Deadly Cost of Missing Contingency Plans
In the first 15–30 minutes after the attack (the golden time window), if there is no targeted contingency plan, the scene will fall into a command vacuum.
Key Step: Network Isolation
If the cellular signal around the stadium is not cut off immediately, the attackers can livestream executions of hostages to pressure the government and receive intelligence about police deployment from accomplices outside. The plan must include one-click authorization to shut down public networks, turning the venue into an information island while retaining only encrypted police communication channels.
Forward Medical Positioning (Triage)
Without a plan, ambulances will be stuck at the outer perimeter. Pre-designated “red zones” for emergency care are essential so that tactical medical teams can enter the hot zone under police cover to perform life-saving bleeding control.

Hostage Control in a Confined Space
Hostages are concentrated and guarded while terrorists establish a temporary stronghold.
3. Counterterrorism Response Process
From perimeter lockdown to lightning assault
Outer Security and Lockdown
1. Establishing a Hard Perimeter
Police cut off traffic in the surrounding area and evacuate people outside the venue. This prevents accomplices from launching secondary attacks (such as vehicle-borne suicide bombs) and stops attackers from blending into the fleeing crowd to escape.
2. Electronic Warfare Engagement
Activate full-spectrum jamming. Shut down cellular and Wi-Fi networks within the stadium, preventing the attackers from communicating externally while maintaining command over secure, encrypted police frequencies.
3. Negotiation and Intelligence Gathering
Use drones with thermal imaging and laser listening devices to probe the interior. Negotiation specialists attempt to establish a single communication channel, buying time and wearing down the attackers’ will.
4. Assault Order (The “Go” Code)
When negotiations collapse, hostages begin to be killed, or intelligence shows that large explosive devices are about to be detonated, the on-scene commander issues the mandatory assault order.
5. Vertical Envelopment
NZ SAS operators use Black Hawk helicopters to fast-rope in (as shown in the image), coordinating with ground teams that breach doors and windows at multiple points. Flashbangs and directional charges are used simultaneously to blind and disorient the enemy.
6. CQB Clearance
Close-quarters battle (CQB) tactics are used to clear rooms one by one and confirm that all threats are neutralized. Tactical medical teams follow closely behind to perform triage on hostages.

Counterterrorism Special Forces Helicopter Assault
4. National-Level Prevention Strategies
How can a country avoid becoming a prime target of terrorist attacks?
Diplomatic Neutrality and Smart Alliances
Avoid deep involvement in overseas conflicts that are highly sensitive in religious or geopolitical terms. Maintain an independent foreign policy to reduce the risk of being targeted for retaliation by extremist organizations because of excessive alignment with a particular great power. Within the “Five Eyes” alliance, focus primarily on intelligence defense rather than offensive roles.
Front-Loaded Border Screening
Strengthen background checks on travelers from high-risk regions and use big-data analysis to identify potential terrorist movement patterns. Conduct strict intelligence cross-checks at the visa-issuance stage to stop threats outside the national border.
Social Integration and De-Radicalization
Eliminate the local soil in which extremism can grow. Strengthen support and integration for immigrant communities to prevent marginalized groups from being infiltrated by foreign extremist ideologies. Establish community-level early warning mechanisms and encourage early reporting of abnormal behavior.
Scenario 2: Proxy War & Naval Blockade (The “Grey Zone”)
Characteristics: Undeclared War, Critical Infrastructure Sabotage, Limited Conflict
Tactical Expansion
The enemy nation is weaker than NZ but supported by a major power (equipment, satellite intel). Utilizing armed civilian ships (“Mosquito Fleet”) and suicide drones for “hit-and-run” harassment.
-
▶
Targets: Marsden Point Oil Depot & Cook Strait Cables. Cutting off fuel supply to the North Island and disrupting inter-island power/comms transmission.
-
▶
Naval Blockade: Laying smart mines off Auckland and Tauranga ports, or using commercial USVs to attack cargo ships. Declaring NZ waters a “War Zone,” causing international insurers to withdraw cover, effectively severing NZ’s maritime lifelines.
-
▶
Strategic Goal: Forcing NZ concessions on EEZ boundaries or demanding the cessation of intervention in specific international affairs.
Defensive Pain Points
- Weak Naval Presence NZ Navy has very few vessels, unable to simultaneously escort merchant ships and sweep for mines.
- Insufficient Energy Reserves Fuel reserves last only weeks; society grinds to a halt once blocked.
- Difficulty Defining War The enemy uses irregular forces and civilian vessels, making it hard for NZDF to strike preemptively without violating international law.
Grey-Zone Conflict and Naval Blockade
PROXY WAR & NAVAL BLOCKADE
Building unmanned-system-based Anti-Access/Area Denial (A2/AD) capabilities to counter undeclared proxy harassment and maritime blockades.
1. Combat Preparation: Stockpiles and Force Build-Up

Individual C4ISR Terminal Integration
Frontline forces are fully connected to the NATO Delta system to synchronize situational awareness.
Strategic Stockpiles
Distributed Fuel and Food Reserves
Use mountainous cave terrain to build dispersed national reserve depots, ensuring at least 6 months of autonomous endurance under a full maritime blockade.
Unmanned Systems Sustainment
Build spare-part stockpiles and 3D-printing workshops to enable rapid repair and modular replacement of frontline equipment, reducing dependence on external supply chains.
Unmanned Combat Force Structure
2. Strategic Objectives: Symmetric Strikes and Deterrence
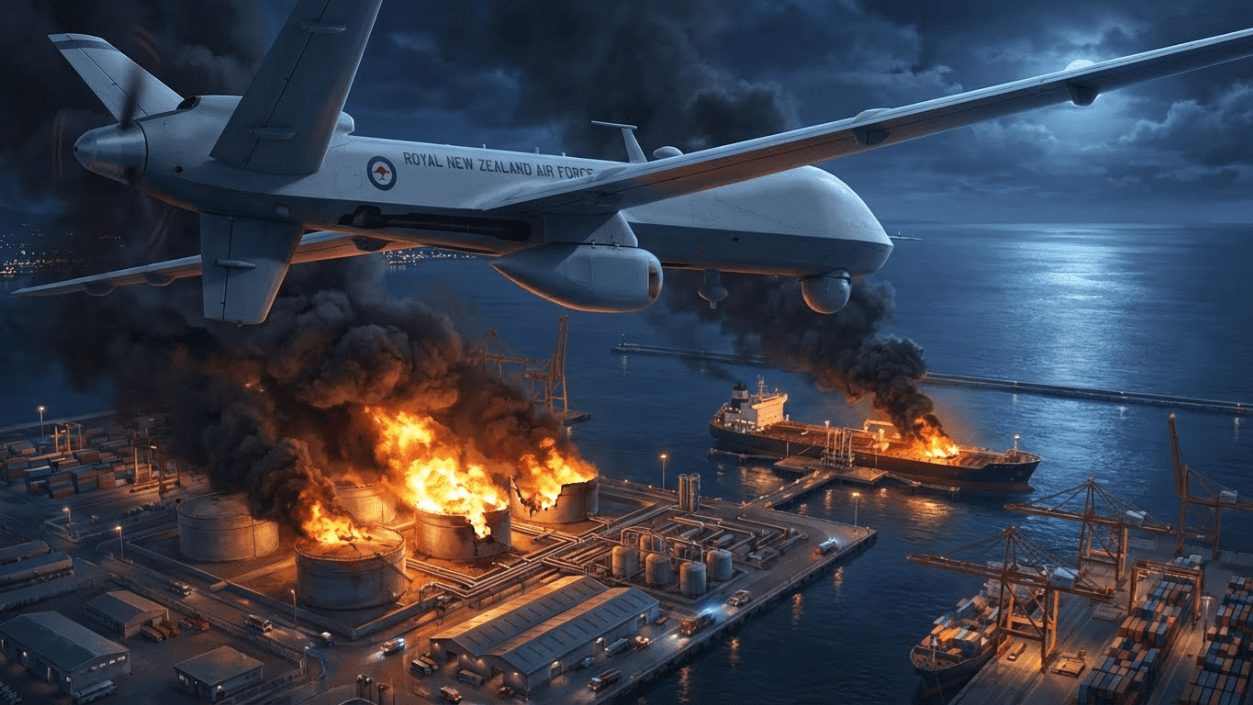
Not Just Passive Defence – Strike at the Source
Use long-range unmanned systems to carry out pinpoint strikes against the enemy’s key ports, cable landing stations and energy nodes. Force the adversary to bear long-term pressure in economic, logistics and manpower losses, creating an unsustainable strategic “sunk cost”.
3. Tactical Execution: Full-Spectrum Blockade and Counterstrike

Far Seas Strikes
- 01. Long-range unmanned aircraft surveil enemy homeland cable zones, ports and surface vessels.
- 02. AI identifies hostile ships and cues semi-submersible unmanned boats and loitering munitions for coordinated strikes.

Near-Seas Blockade
- 01. Medium-range ISR/strike drones coordinate with manned fighters to control the area.
- 02. Establish a 200-kilometre exclusion zone; any vessel within the zone that refuses inspection is classified as an enemy ship and sunk.

Port Defense
- 01. Deploy counter-drone gun arrays and underwater acoustic sensor networks.
- 02. Smart minesweeper boats conduct day-and-night clearance to ensure the security of lifeline supply routes.
Information Operations Synchronisation (Info Ops)
Package and publish records of each strike, and brief Five Eyes / the United Nations / ASEAN in sync to secure legitimacy and external support.
4. Victory Metrics
Tactical Victory
Enemy ports are paralysed, enemy forces withdraw or proactively request negotiations.
Sovereignty Protection
Merchant shipping routes are restored, and key sea lanes are cleared of mines and interference.
Information Dominance
International mainstream media recognise New Zealand as the defending party, and the adversary is diplomatically isolated.
Control Consolidation
A complete unmanned defence system is established from port to inland to far seas.
Scenario 3: Major Power Surprise Attack (The “Trojan Horse”)
Characteristics: Disguised Assembly, Decapitation Strike, Urban Control
Tactical Expansion
Using global supply chains as cover to disguise elite troops and missile launch systems as standard shipping containers. Multiple seemingly ordinary cargo ships dock simultaneously at Auckland, Wellington, and Lyttelton ports.
-
▶
Zero Hour Action: Late at night, containers on ships open, firing cruise missiles to precisely destroy the Beehive (Parliament), Ministry of Defence HQ, and Whenuapai Airbase runways.
-
▶
Troop Deployment: Mechanized infantry hidden in containers rapidly seize port areas, using them as beachheads to advance into city centers and capture comms nodes (e.g., Spark and One NZ data centers).
-
▶
Hostage Strategy: Blocking the Auckland Harbour Bridge and major motorways, using the million-plus population as “human shields” to threaten city destruction if allies (AUS/US) intervene.
-
▶
Strategic Goal: Using NZ as a bargaining chip to force Western alliance concessions in other geopolitical conflicts (e.g., Taiwan Strait or Eastern Europe), or to permanently neutralize NZ.
Defensive Pain Points
- Port Security Gaps Customs inspects a tiny percentage of containers and lacks capability to detect military-grade radiation or heat signatures.
- Centralized Administration Wellington’s geography is enclosed; once the port and airport are seized, the government is trapped.
- Lack of Heavy Weapons NZDF lacks tanks and attack helicopters, making it difficult to retake seized port facilities in urban combat.
“Trojan Horse” Port Surprise Attack
MAJOR POWER SURPRISE ATTACK
High-intensity homeland combat: An extreme scenario in which the enemy uses container RoRo and cargo ships as disguise to infiltrate, strike ports by surprise, and seize key cities. A full-spectrum simulation of tactical procedures from early warning and preparation to counterattack and annihilation.
1. Threat Assessment: Disguise and Surprise

The “Trojan Horse” Hidden in Containers
Disguised civilian ships rush into the port; air-defense missiles and armored vehicles deploy rapidly.
Enemy Strategic Intent
The adversary attempts to launch a surprise attack under “war without declaration”, seize large numbers of civilians as human shields, and thereby pin down Western alliance attention and military resources away from the Asian theatre. The tactical core is “multiple simultaneous landings”, with coordinated assaults on New Zealand’s three main port cities.
Follow-on Threat
Additional disguised cargo ships loaded with weapons and reinforcements remain at sea, awaiting the establishment of a beachhead before launching a second wave. These must be intercepted and cut off before they can dock.
2. Pre-War Preparation: Nation in Arms & System Redundancy
Fielding Unmanned Forces
Form operational units of unmanned semi-submersible combat boats, long-range early-warning/strike drones, and unmanned ground combat vehicles.
Mountain Distributed Stockpiles
Use natural caves to build national-level strategic depots, storing fuel and grain for six months. Maintain one year’s worth of spare parts for drones and electronic-warfare equipment to withstand a prolonged blockade.
Delta Platform Integration
Connect all military systems to the Delta platform; increase communications and command-node redundancy to threefold, and establish unbreakable information-sharing links with the Five Eyes alliance.
Drone Pilot Militia Mobilisation
Maintain a registered base of 3,000+ drone pilots, with at least 1,000 trained on military-grade systems. In peacetime they are civilians; in wartime they receive authorisation to draw weaponised drones from secure depots.
Infrastructure Resilience & Dispersed Basing
Prepare highways as emergency runways and disperse weapons and equipment so they cannot be destroyed in a single first strike.

Dismounted Digital Terminals & Drone Teaming
3. Tactical Execution: Counterattack & Encirclement
Striking at the Source: Cut Off Supply
Once enemy concentration is detected, do not hesitate. Use C-130 transport aircraft to drop glide-guided bombs from outside the enemy air-defense envelope, directly striking the enemy “mothership” vessels in port.
- ✓ Sink troop-carrying ships
- ✓ Destroy ammunition and logistics depots
- ✓ Block port entrances and exits

Enemy vessels in port destroyed by precision strike

Evacuation & Communications Restoration
Enemy advance parties will almost certainly sabotage communications and seize essential civil infrastructure. Our forces must act rapidly to minimise civilian casualties.
- Quickly evacuate civilians to non-combat zones to avoid hostage crises.
- Activate reserve communications facilities to ensure the population can receive evacuation and safety instructions.
- Use broadcast channels to call civilians away from key target areas.
200 km Maritime Exclusion Zone
Deploy naval and air assets to comprehensively clear the surrounding waters and cut off any further landing attempts.

Heliborne special operations assault
Grid Encirclement (The Siege)
Call up reservists and trained drone pilots back into their wartime units. Avoid frontal assaults; instead, establish roadblocks and implement grid-based control of urban areas.
Deliberately expose attractive but hardened targets to draw the enemy out of cover into attacking well-prepared strongpoints.
Once enemy elements are segmented and encircled, conduct full-spectrum jamming to sever their internal communications.
After prolonged attrition, herd the remaining enemy towards open waterfront or port areas and use concentrated heavy firepower to finish them off.
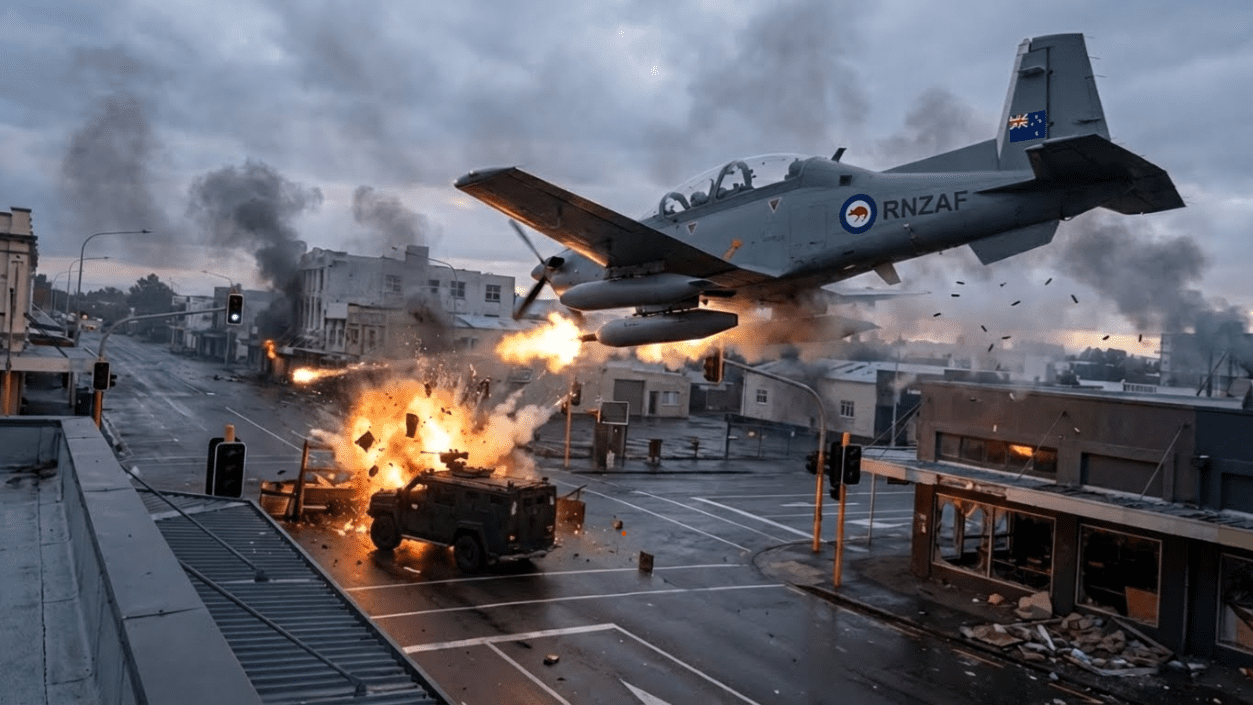
Trump Card: C-130 “Flying Arsenal”
To offset the limited payload of New Zealand’s fixed-wing combat aircraft, employ C-130 transport aircraft as improvised heavy strike platforms.
- 💣 Directly airdrop glide-guided bombs from the cargo bay
- 🚢 Achieve the ability to sink 30,000-ton-class ships
- 🛡️ Stand-off strike to keep the aircraft outside enemy air-defense envelopes
Firepower Delivery Comparison
Firepower effectiveness +300%+
Scenario 4: Unrestricted Warfare & Social Collapse (The “Invisible Enemy”)
Characteristics: Unknown Origin, Limitless Sabotage, Economic & Psychological War
Tactical Expansion
Not seeking military occupation, but continuous, random sabotage to plunge NZ society into chaos, collapse the economy, and destroy trust in government. A war with “no smoke but fire everywhere.”
-
▶
Economic Heart Attack: Poisoning (or spreading rumors of poisoning) the dairy supply chain targeting Milk, leading to international bans on NZ exports and instant economic shock.
-
▶
Ecological Terrorism: During dry summer periods, using drones to drop incendiary devices into commercial forests in the South Island and central North Island, starting uncontrollable wildfires that exhaust fire and military resources.
-
▶
Transportation Severance: Sabotaging Interislander ferry facilities or rail bridges to cut North-South logistics. Causing explosions or chemical leaks in major tunnels (e.g., Waterview Tunnel).
-
▶
Cyber & Financial Destruction: Attacking bank settlement systems to wipe citizen deposit data; attacking power grid SCADA systems to cause frequent blackouts.
Defensive Pain Points
- Attribution Difficulty Enemy uses proxies or cyber attacks; government struggles to identify the real culprit for retaliation, remaining passive.
- Impossible to Defend Everything Forests, farms, and grid pipelines stretch thousands of kilometers, impossible to physically guard 24/7.
- Fragile Social Resilience High reliance on digital payments and logistics; once interrupted, urban life collapses rapidly.
Threat Response Difficulty & Resource Requirement Analysis
Strategic Insight
Against these four scenarios, traditional “Big Gun, Big Ship” defense systems are ineffective. Whether facing terrorists in crowds, sea drones harassing shipping, container missiles in ports, or arson drones in forests, New Zealand must establish an asymmetric defense network based on “Full-Domain Awareness (Delta System),” “Rapid Response (FPV Swarms),” and “Total Defense.” Only by utilizing low-cost, high-coverage unmanned systems can NZ compensate for its massive military and geographical vulnerabilities.